Runtime Security
STOP ATTACKS
IN REAL TIME
Runtime security for your
Apps
Cloud
workloads
AI
Agents
Apps

Every
Second
Counts
BOOK A DEMO
The window between vulnerability disclosure and active exploitation is collapsing. Recent AI systems like Anthropic's Mythos have shown that discovering and chaining exploits at machine speed is no longer hypothetical.
Patching cycles and periodic scans cannot scale to that pace. To protect what matters, organizations must move from passive visibility to active runtime protection, understanding and defending what's actually running across applications, infrastructure, and AI.
Rapid deployment. Runtime security. Proven performance.
Cloud Application
Detection and
Response
Learn more
Learn more
→
→
Runtime
Vulnerability
Menagment
Learn more
Learn more
→
→
Runtime AI
Security
Learn more
Learn more
→
→
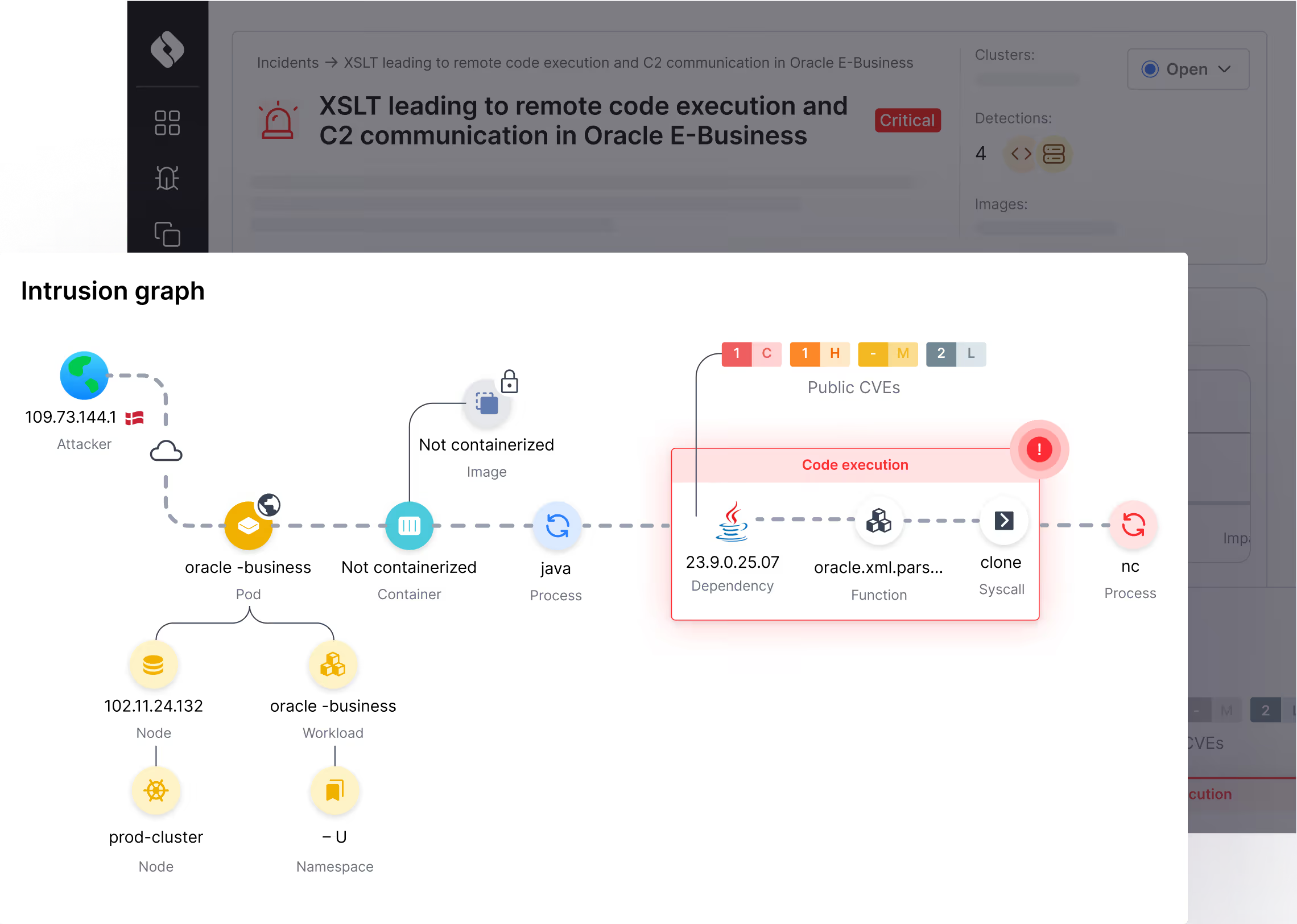
Protect against exploits across apps, workloads, hosts, and cloud infrastructure.
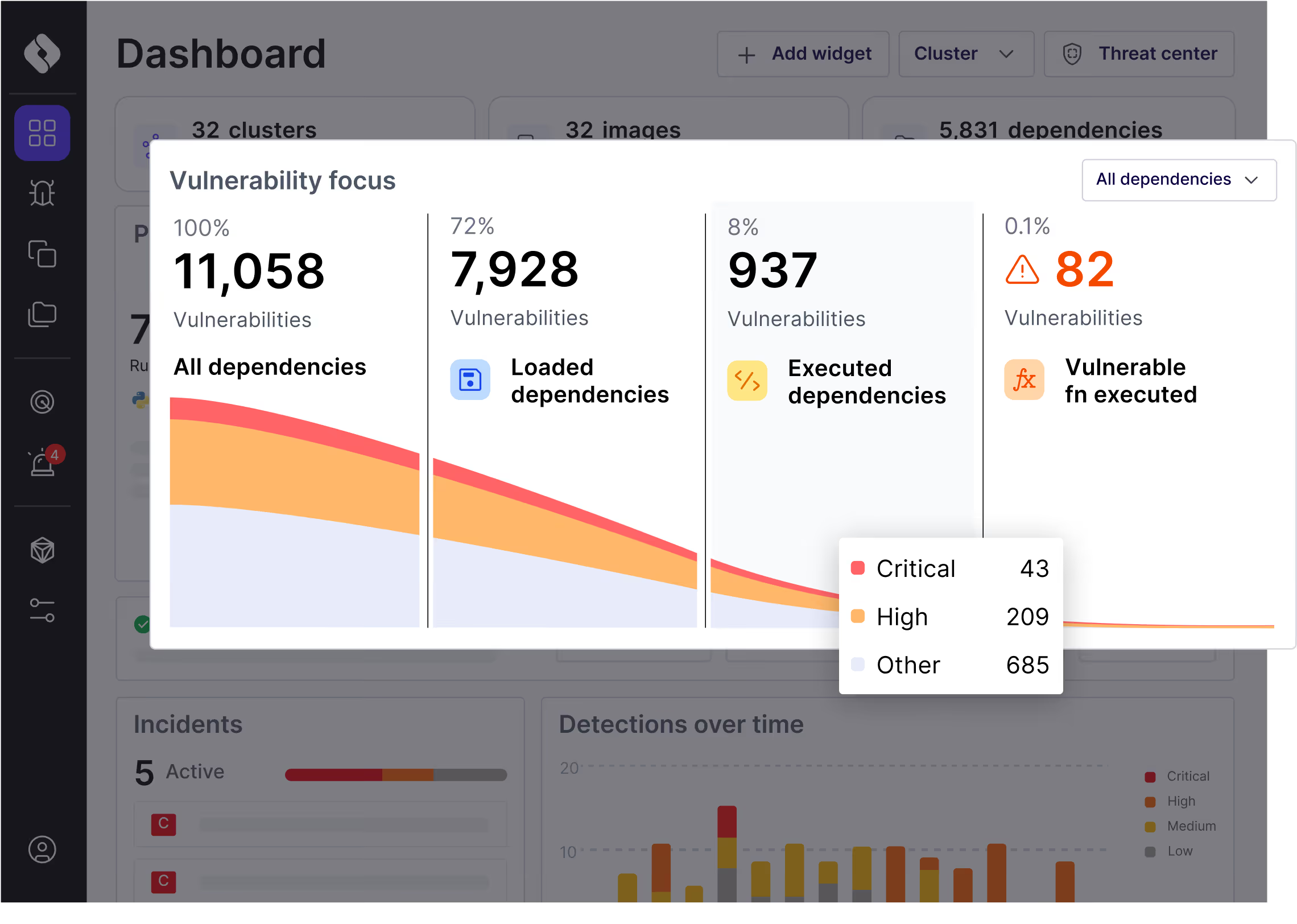
Cut down vulnerability noise 90%+ with runtime proof of exploitability
Protect LLMs and AI agents wherever they're tested and run.
Our Runtime Advantage
Catch
Catch Attacks Early
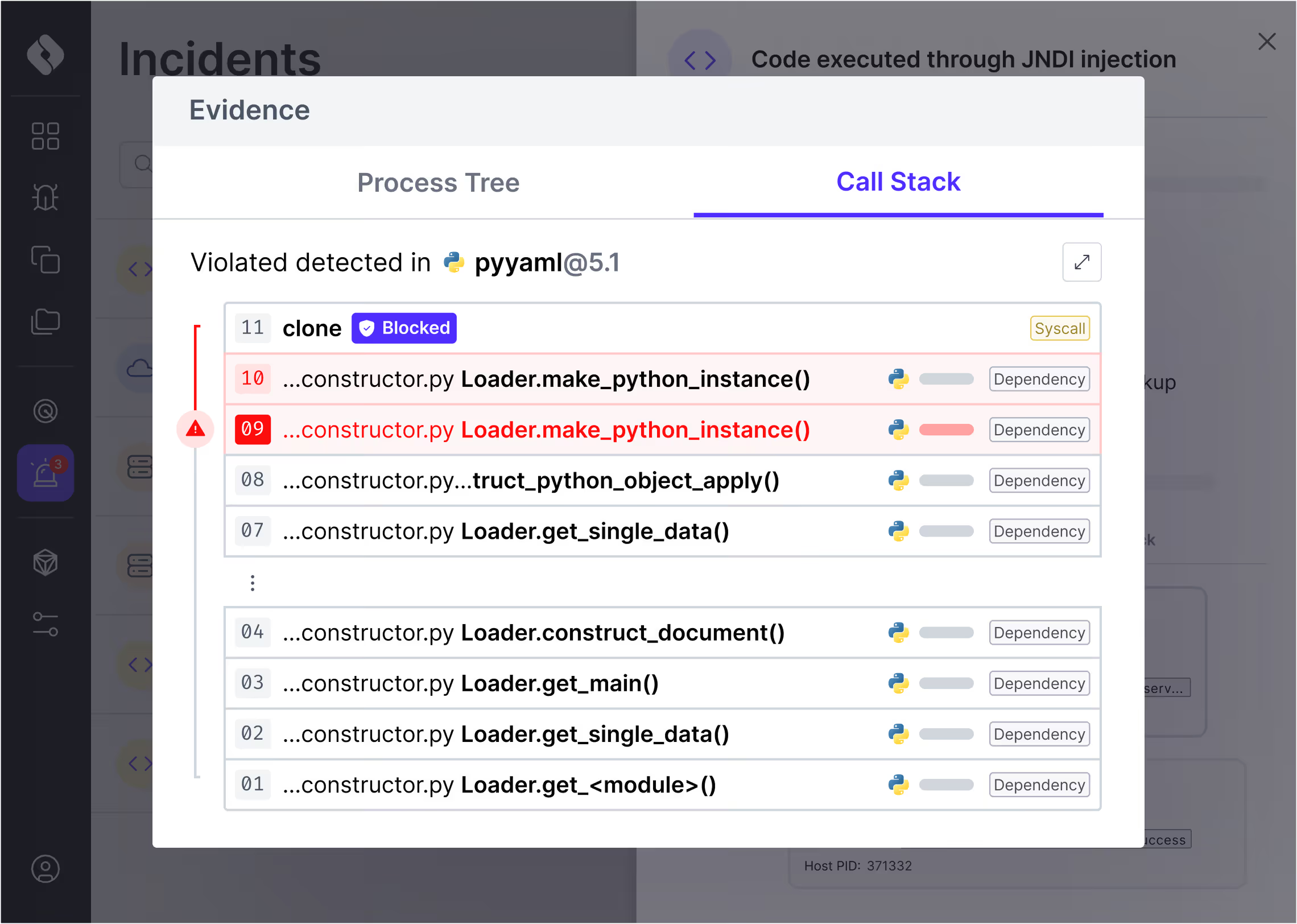
Detect exploits at the application layer, where attacks begin, and stop them before damage spreads.
Prove Exploitability
See which vulnerabilities actually execute in runtime, eliminating 90-99% of noise.
prove
block
Block Threats Safely
Block malicious functions precisely, keeping applications safe and business running.
The Oligo runtime security platform
Slash vulnerability noise & stop modern attacks
App Security
• Runtime SCA & SBOM
• Licensing Complience
• CVE Noise Reduction
• Licensing Complience
• CVE Noise Reduction
Cloud Security
• Workload Protection
• Container Scanning
• Container Scanning
AI Security
• AI Security Posture Management
• AI Detection and Response
• AI Detection and Response
SecOps
• Threat - Vuln Enrichment
• Attack Mitigations
• Forensics
• Attack Mitigations
• Forensics
Prevent supply chain attacks
Zero-day response
Minimize exploitability
Stop attacks

Lightweight Sensor
AI
App / Code
Cloud / Host
Network
Why organizations choose Oligo
oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME .
oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME .
Don't just scan passively.
Protect actively with Oligo.
BOOK A DEMO
oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME .
oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME . oligo security . runtime security . STOP ATTACKS IN REAL TIME .