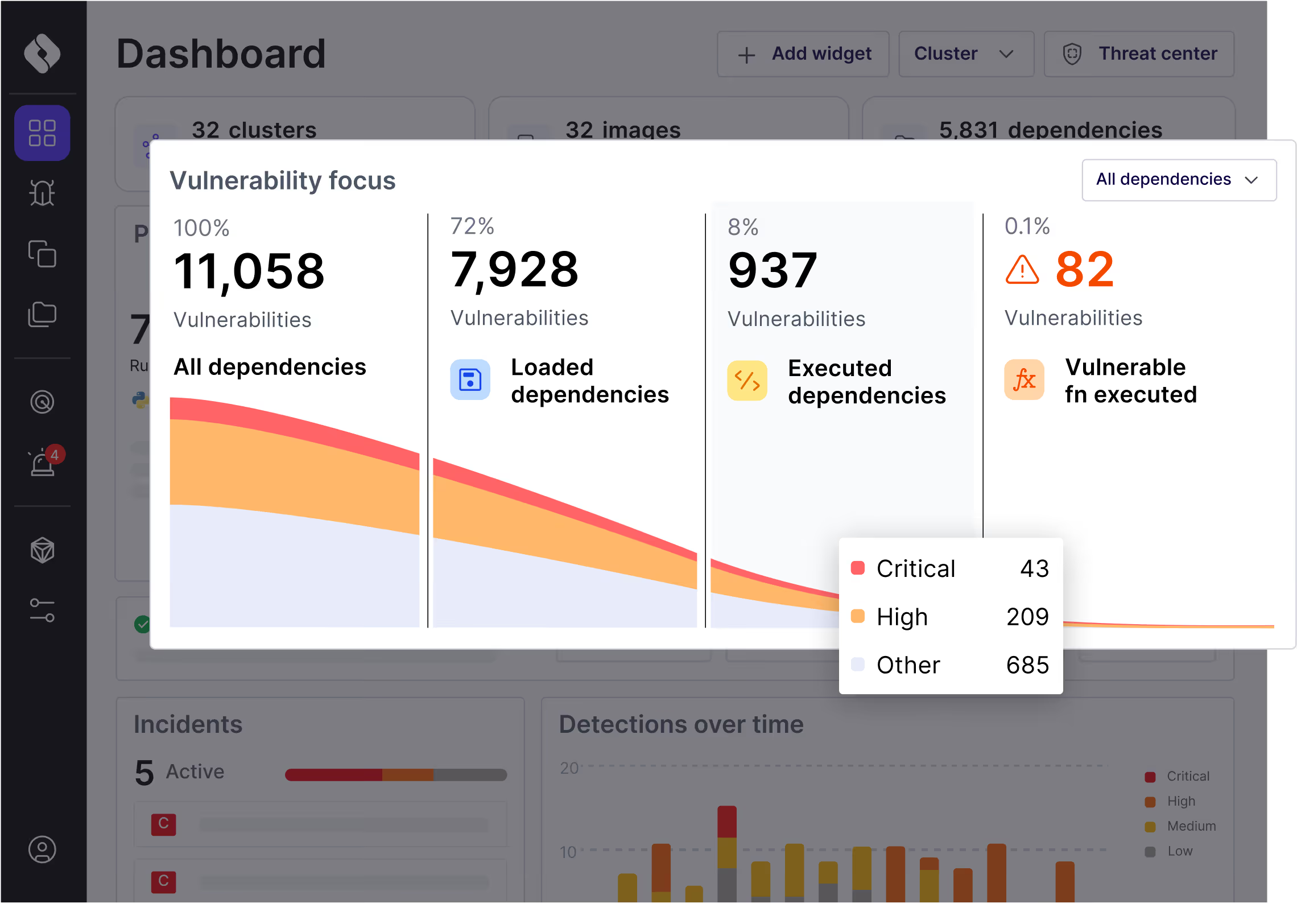
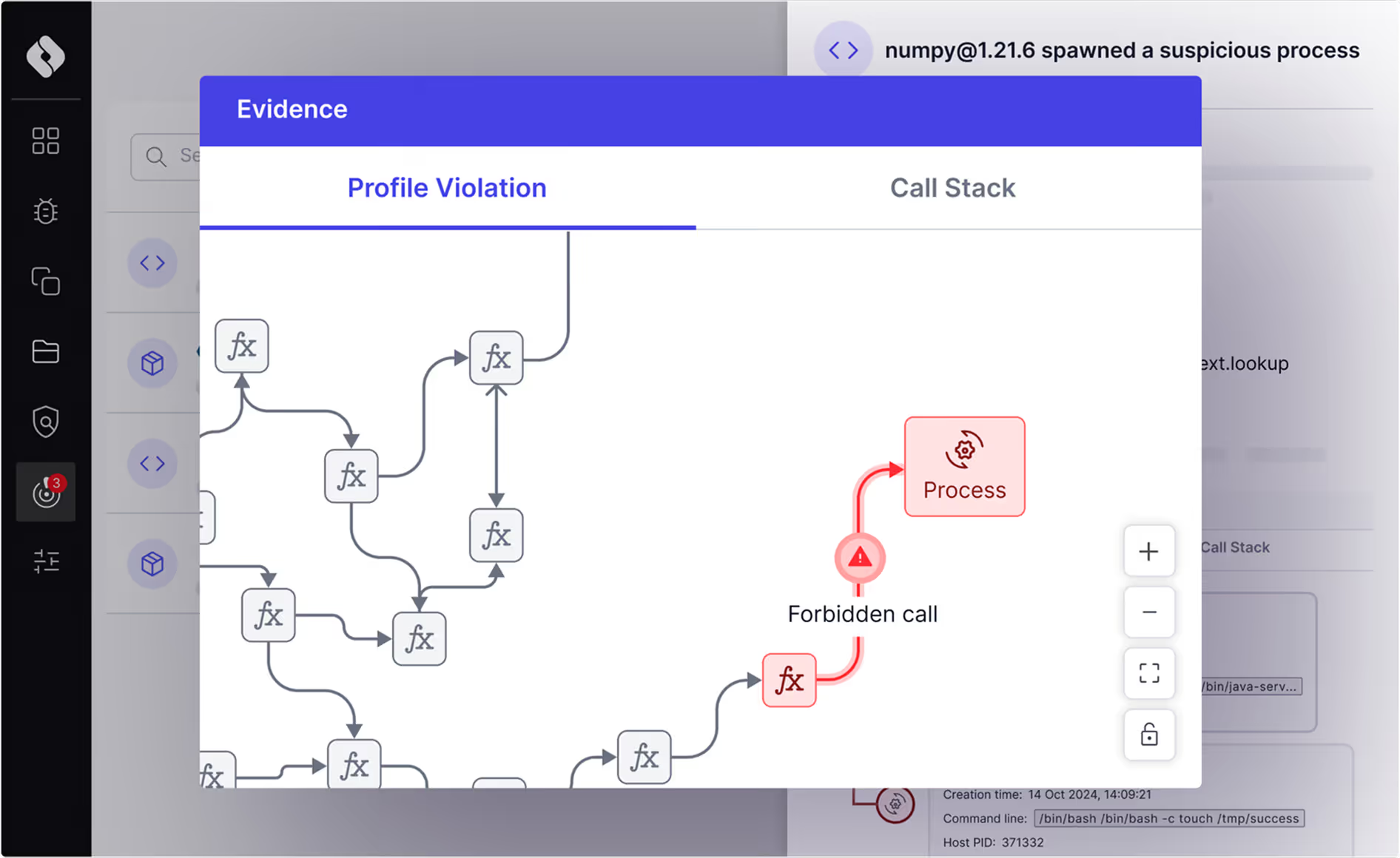
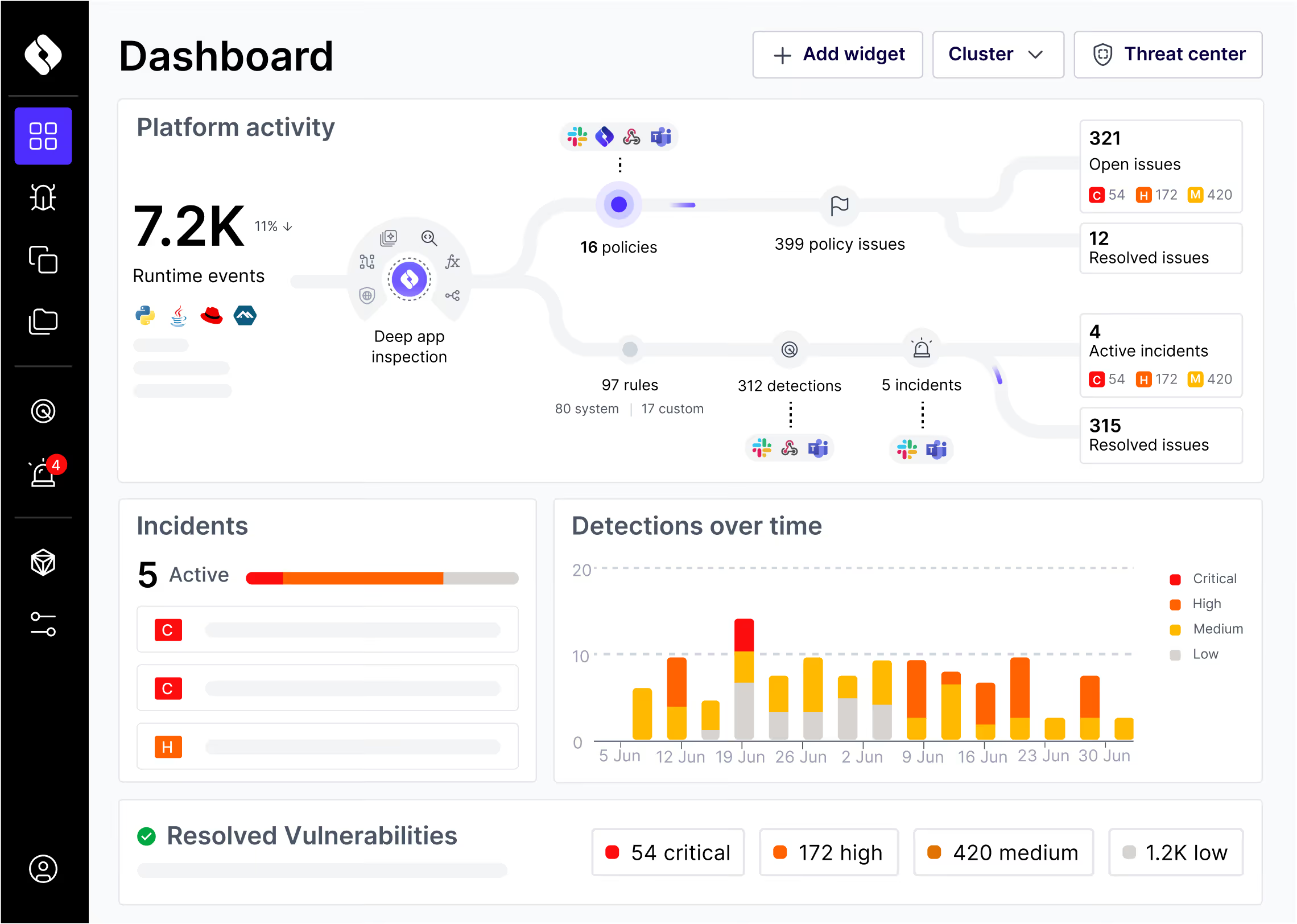
Beyond Severity: Focus on Exploitability
When is a “critical” vulnerability really critical? When it’s executed at runtime, allowing it to be exploited by attackers.
Oligo’s unique sensor detects which libraries and individual functions are executed, so you can identify real risks and stop chasing false positives for good.
Oligo’s unique sensor detects which libraries and individual functions are executed, so you can identify real risks and stop chasing false positives for good.
.svg)