Best Runtime Security Tools: Top 8 Options in 2026

What Are Runtime Security Tools?
Runtime security tools are software that monitors and protects applications and systems in real time by analyzing their behavior to detect and stop threats as they happen. They work by observing system calls, network activity, and process behavior, then comparing them against a baseline of normal activity to identify anomalies and potential attacks like malware injection, privilege escalation, and container breakouts.
Key functionalities include:
- Threat detection: Monitors system calls, network events, and command executions in real-time to identify unusual behavior and flag it as a potential threat.
- Incident response: Provides detailed logs of system activities, which helps security teams investigate incidents, understand attack timelines, and determine the full scope of a compromise.
- Anomaly detection: Builds a profile of "normal" application or system behavior and alerts on any deviations from that profile.
- Policy-driven controls: Enforces security policies by controlling access and preventing unauthorized actions, such as a container attempting to access sensitive files.
- Deep visibility: Enables teams to visualize system behavior, including calls, file activities, and network connections.
- Protection against various attacks: Defends against threats that manifest after deployment, such as malware activation, privilege escalation, and container breakouts.
- Integration: Works integrate seamlessly with other tools in the security and operational stack, including SIEM and SOAR.
This is part of a series of articles about application security.
Key Capabilities of Runtime Security Tools
Threat Detection
Threat detection forms the core of any runtime security tool, focusing on identifying potentially malicious activities as they happen within the system. This is achieved through real-time monitoring, signature-based detection, and behavioral analytics that flag known threats such as malware, ransomware, or privilege escalation attempts.
Runtime threat detection isn't limited to known attack patterns; it also involves correlating system calls, network flows, and file access patterns to spot unusual or high-risk behaviors. This enables the detection of advanced or previously unknown threats, providing defenders with actionable alerts that go beyond traditional rule-based approaches.
Incident Response
Incident response in the context of runtime security tools refers to the automated or orchestrated actions that occur after a threat or anomaly is detected. These reactions can include alerting relevant personnel, killing rogue processes, isolating compromised containers or hosts, or enforcing policy-based controls to stop lateral movement.
Automation is increasingly leveraged to ensure a rapid and consistent incident response. Predefined playbooks can assist in containing threats with minimal manual intervention, reducing both risk and the burden on security teams. Good runtime security tools allow customization of responses, ensuring they align with the organization's unique risk tolerances and operational contexts.
Anomaly Detection
Anomaly detection extends the capabilities of runtime security tools by highlighting deviations from established behavioral baselines, not just known bad signatures or rule violations. This involves continuously profiling application, system, and network behaviors, and flagging activities or patterns that fall outside expected norms. Such anomalies could indicate credential misuse, insider threats, or stealthy attacks designed to evade traditional defenses.
Advanced anomaly detection relies on machine learning and analytics, adapting to evolving workloads and user behaviors. The ability to detect subtle, context-specific anomalies gives organizations an edge in identifying novel threats and operational issues before they escalate. When coupled with meaningful alerting and context-rich incident details, this approach reduces noise.
Policy-Driven Controls
Policy-driven controls are configurations and rules defined by administrators to determine how runtime security tools should monitor and respond to specific events within the environment. These policies may include permitted applications, approved network connections, and allowable system calls. By enforcing these policies, runtime security tools limit the attack surface by preventing unauthorized or unintended behaviors.
These controls not only offer granular visibility into operations but also form the basis for compliance and organizational governance. They can be dynamically updated as the environment evolves, ensuring that protection adapts to changes in application architecture or regulatory requirements.
Deep Visibility Across the Runtime Environment
Deep visibility refers to the comprehensive monitoring capabilities of runtime security tools, which inspect system calls, file activities, network connections, and process behaviors across all runtime resources. This level of insight allows security teams to understand exactly what is happening in any part of a dynamic infrastructure at any given time. Such depth is critical for detecting stealthy threats, investigating incidents, and performing effective root cause analyses.
With deep visibility, runtime security tools provide context-rich data to distinguish between benign and suspect activities. This granularity ensures that even sophisticated attacks like fileless malware or privilege escalation within containers are uncovered and managed in real time.
Protection Against Various Attacks
Runtime security tools guard against a wide range of attacks, from privilege escalations and lateral movement to container escapes, malware injections, and data exfiltration. By leveraging a combination of behavioral monitoring, policy enforcement, and anomaly detection, these tools address both known threats and novel attack vectors tailored to dynamic cloud-native environments.
These tools also help mitigate risks presented by vulnerabilities that may not be patched immediately, providing a vital layer of defense in fast-moving development pipelines. By blocking suspicious activity at runtime or alerting relevant teams for instant investigation, organizations reduce the window of exposure from newly discovered threats, making it harder for attackers to achieve their goals within the infrastructure.
Integration with Broader Security and Operations Stack
Modern runtime security tools are not standalone products; they are intended to integrate seamlessly with existing security and operational systems, such as SIEM, SOAR, and IT service management platforms. This integration ensures that threat data and incident information flow smoothly across workflows, promoting more effective detection, response, and compliance management.
Such interoperability enables security teams to correlate runtime intelligence with data from other parts of the stack, gaining a holistic view of risk across the organization. Effective runtime tools offer APIs, out-of-the-box connectors, and extensibility, reducing deployment friction and helping organizations maximize the value from their broader security investments.
Related content: Read our guide to application detection and response
Notable Runtime Security Tools
1. Oligo
Oligo is a Cloud Application Detection and Response (CADR) platform built on Deep Application Inspection (DAI): a sensor technology that monitors code execution and OS activity simultaneously at the application layer. Where every other tool on this list observes system calls, process starts, and network connections from the outside, Oligo sees the specific function call inside a running application that triggered each syscall. That distinction matters because most attacks originate at the application layer, not the infrastructure layer — and no infrastructure-layer sensor can see them as they begin.
Oligo deploys a single lightweight agent per host with no source code access required and no changes to running applications.
Key features include:
- Deep Application Inspection: Monitors live function calls, dependency execution, API activity, and OS interactions in real time across first- and third-party applications, without instrumentation or source code access.
- Proof of exploitability: Identifies which CVEs are loaded and actively executed at runtime, not just present in a scan. Teams typically see a 90–99% reduction in actionable vulnerabilities within 48 hours of deployment.
- Contextual Blocking: Blocks exploit attempts by sandboxing the specific syscalls an attack requires, correlated to the function call that preceded them. Applications continue running without downtime; no container kill required.
- CVE virtual patching: Protects against known vulnerabilities while patches are pending by blocking the underlying attack technique, covering entire classes of CVEs with a single policy.
- Runtime AI security: Tracks AI frameworks, models, inference servers, and agentic workflows executing in production, building a live AI-BOM and detecting anomalous agent patterns at the execution layer.
CADR for cloud and application layers: Correlates exploit and post-exploit activity across networks, workloads, hosts, and cloud environments, giving security teams root-cause visibility rather than symptom-level alerts.
2. Palo Alto Cortex Cloud
Cortex Cloud provides runtime protection for VMs, containers, and serverless workloads in cloud-native environments. It uses a cloud-optimized detection and response agent that reduces resource usage while delivering alerts.
Key features include:
- Cloud runtime protection: Detects and blocks threats in real time across diverse cloud workloads using a cloud-optimized agent
- Unified command center: Centralizes visibility and control across runtime, posture, and application layers
- Flexible resource usage: Reduces agent footprint and CPU consumption based on workload requirements
- Integrated detection and response: Correlates runtime events with cloud identity and configuration data for context-aware threat response
- Accelerated onboarding: Simplifies deployment with rapid account integration and a user interface

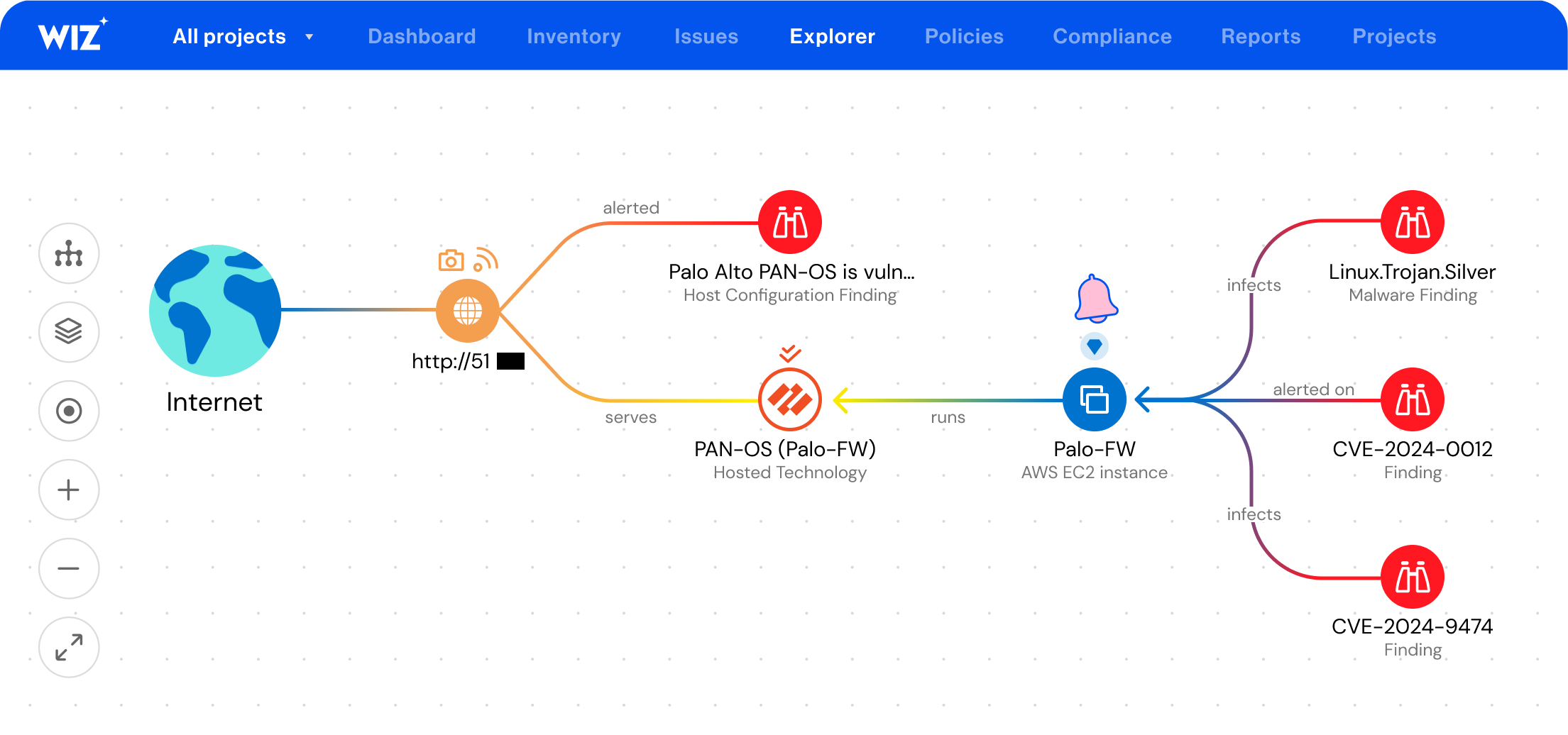
3. Wiz Defend
Wiz Defend is a runtime detection and response solution that combines eBPF-based telemetry with cloud and SaaS context to identify and respond to threats across containers, VMs, and serverless environments. It correlates signals across the stack to detect attacker behaviors, then enables remediation through automated playbooks and root-cause analysis.
Key features include:
- eBPF-powered runtime monitoring: Uses a lightweight sensor to observe workload activity without introducing performance overhead
- Behavioral detection: Identifies anomalies using baselining and threat intelligence across containers, Kubernetes, and cloud services
- Cloud-native containment: Automates remediation using root-cause analysis and pre-built response workflows
- Cross-layer correlation: Links runtime events with identity, data access, and configuration context for precise threat assessment
- Runtime file integrity and drift detection: Monitors for unauthorized changes and indicators of compromise across containerized environments
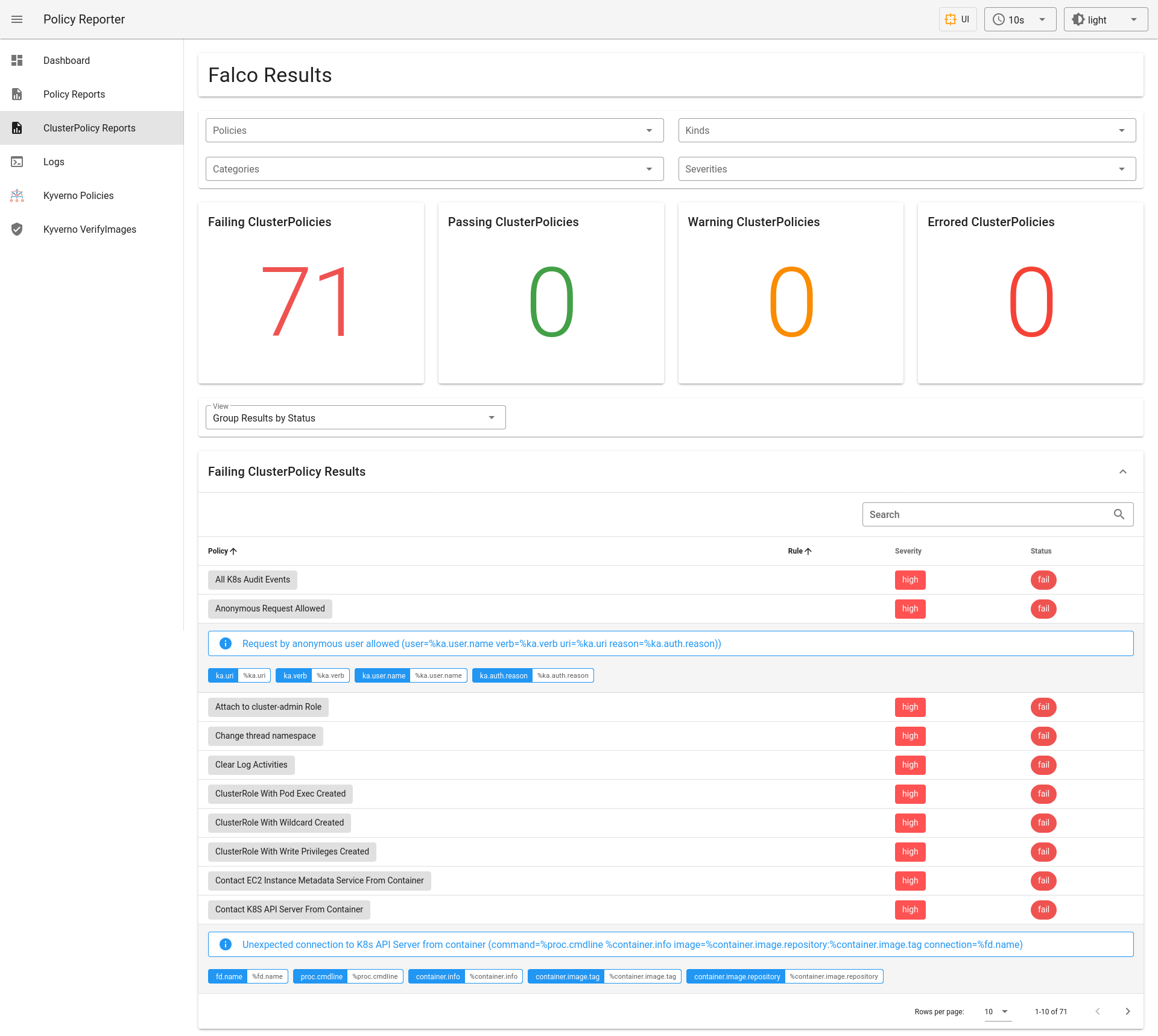
4. Falco
Falco is an open source runtime security tool built for cloud-native environments. It monitors system activity using eBPF and kernel events to detect unexpected behavior across hosts, containers, Kubernetes clusters, and cloud services. By applying a customizable set of rules, Falco identifies abnormal activity, such as privilege escalation, unauthorized network access, or changes in system configuration, and alerts security teams.
Key features include:
- eBPF-based detection: Uses eBPF to observe system calls and detect malicious activity at the kernel level
- Custom rules engine: Comes with ready-to-use detection rules that can be tailored to match organizational policies
- Real-time alerting: Provides streaming alerts for suspicious behavior, configuration drift, and policy violations
- Kubernetes and cloud native integration: Monitors activity in Kubernetes, containers, and cloud services via plugins
- Extensive ecosystem integration: Supports integration with over 50 third-party tools for alert forwarding and incident response
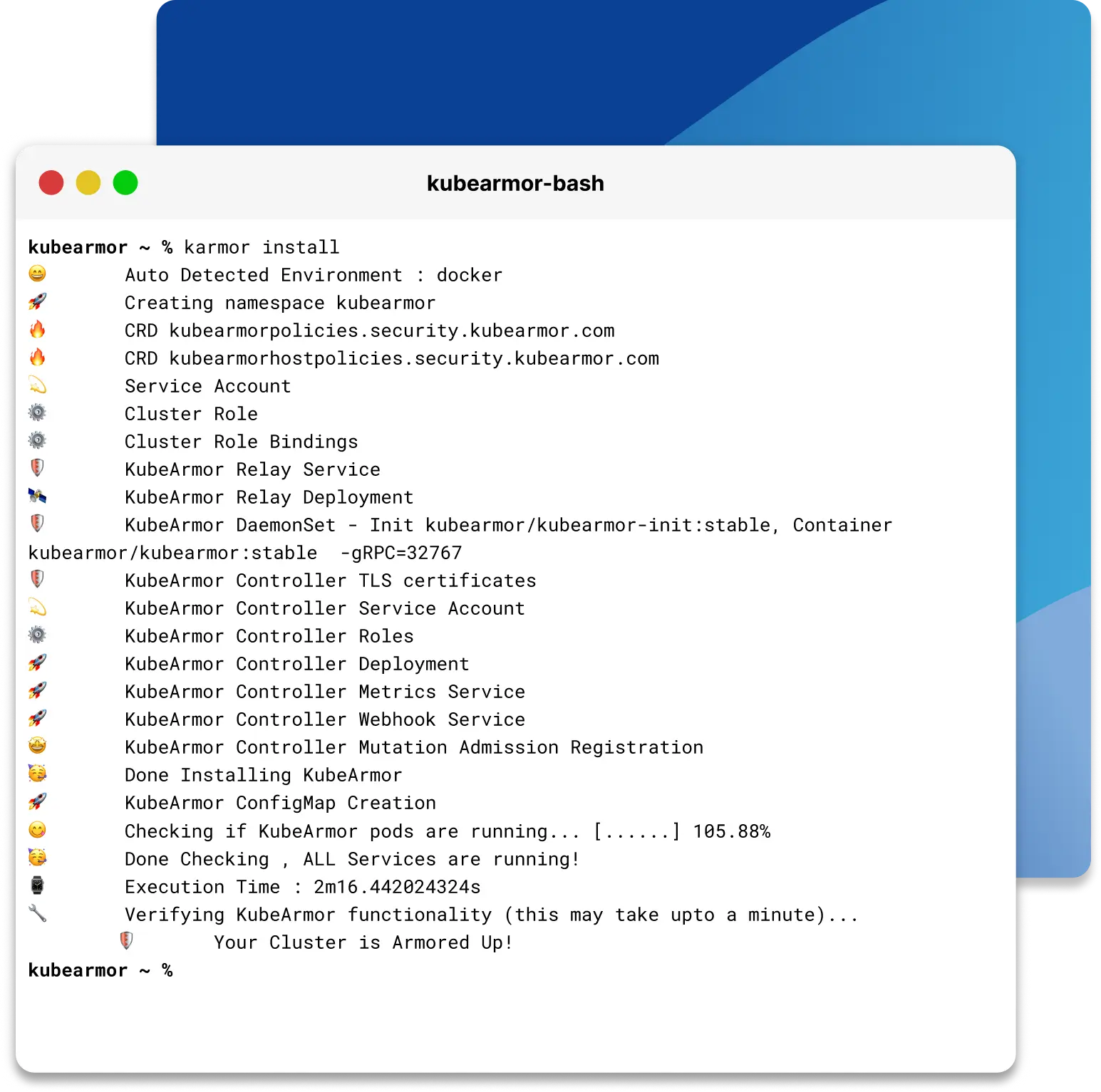
5. KubeArmor
KubeArmor is a runtime security enforcement engine for Kubernetes and cloud-native environments. It uses eBPF and Linux security modules (LSMs) like AppArmor, SELinux, and BPF-LSM to enforce security policies within workloads, without requiring changes to containers or host systems.
Key features include:
- Inline runtime mitigation: Blocks malicious activity in real time using LSMs, preventing execution instead of reacting after the fact
- eBPF and LSM integration: Uses eBPF and Linux security modules for efficient, low-overhead policy enforcement
- Kubernetes-native policies: Supports policy definitions using Kubernetes metadata, aligning enforcement with Kubernetes constructs
- Behavior restrictions: Controls process execution, file access, networking, and resource usage within workloads
- Policy violation logging: Captures and logs policy breaches, offering visibility into runtime behavior
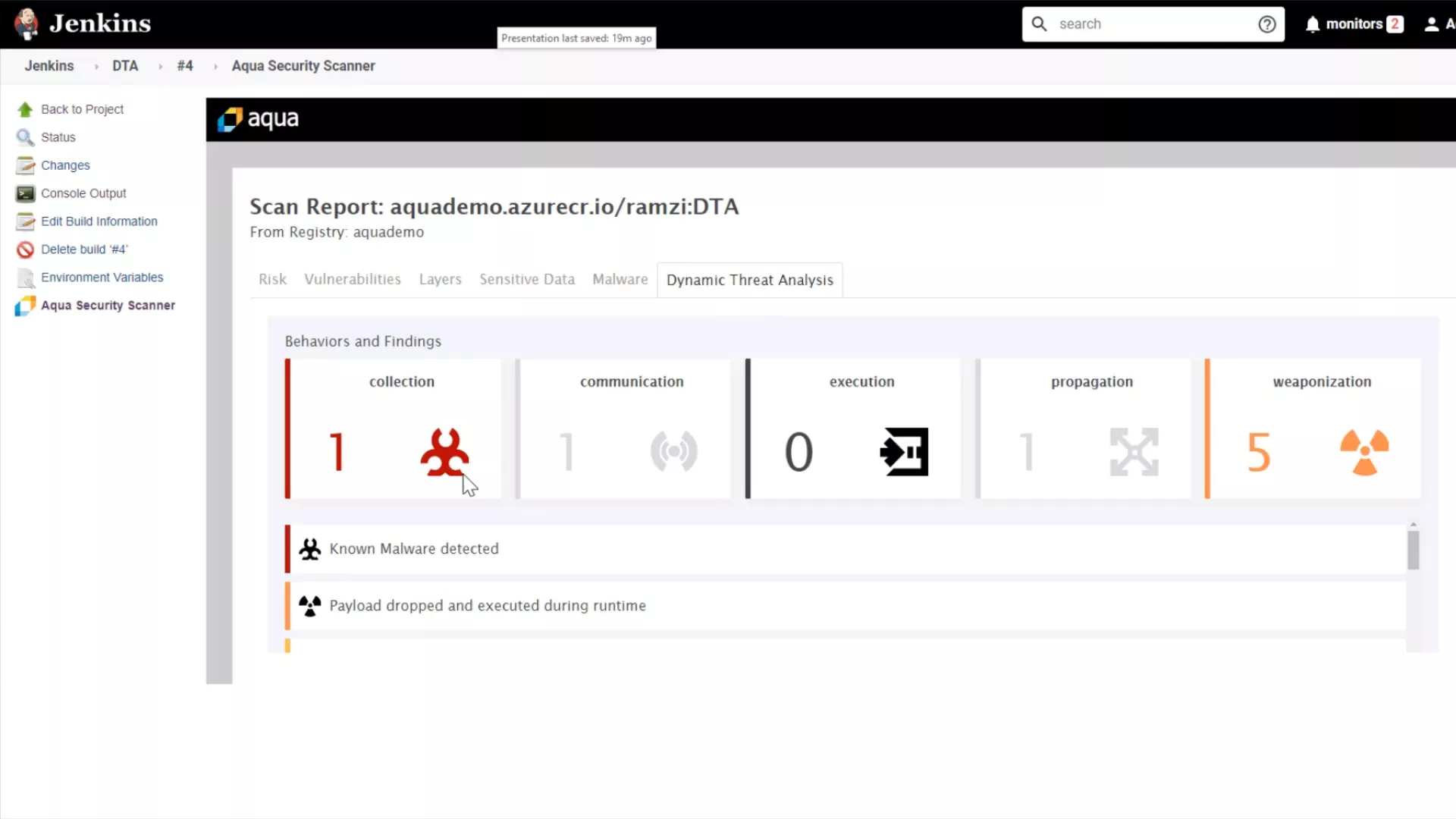
6. Tracee
Tracee is an open source eBPF-based runtime security engine developed by Aqua Security. It collects detailed system events and applies curated detection rules to identify suspicious behavior in containerized and Linux environments. Tracee emphasizes behavioral indicators based on attacker tactics and provides flexible integration and deployment options.
Key features include:
- eBPF event collection: Gathers over 330 syscall and kernel events for visibility without relying on kernel modules
- Behavioral detection rules: Detects evasion techniques such as fileless execution or anti-debugging based on MITRE ATT&CK patterns
- Easy deployment and portability: Runs with a single command and supports CO:RE mode for compatibility across Linux versions
- Custom filtering and alerting: Allows control over what events to monitor and how to format output
Integration support: Sends alerts to external systems like Slack or GitHub via tools like Postee
7. Cilium
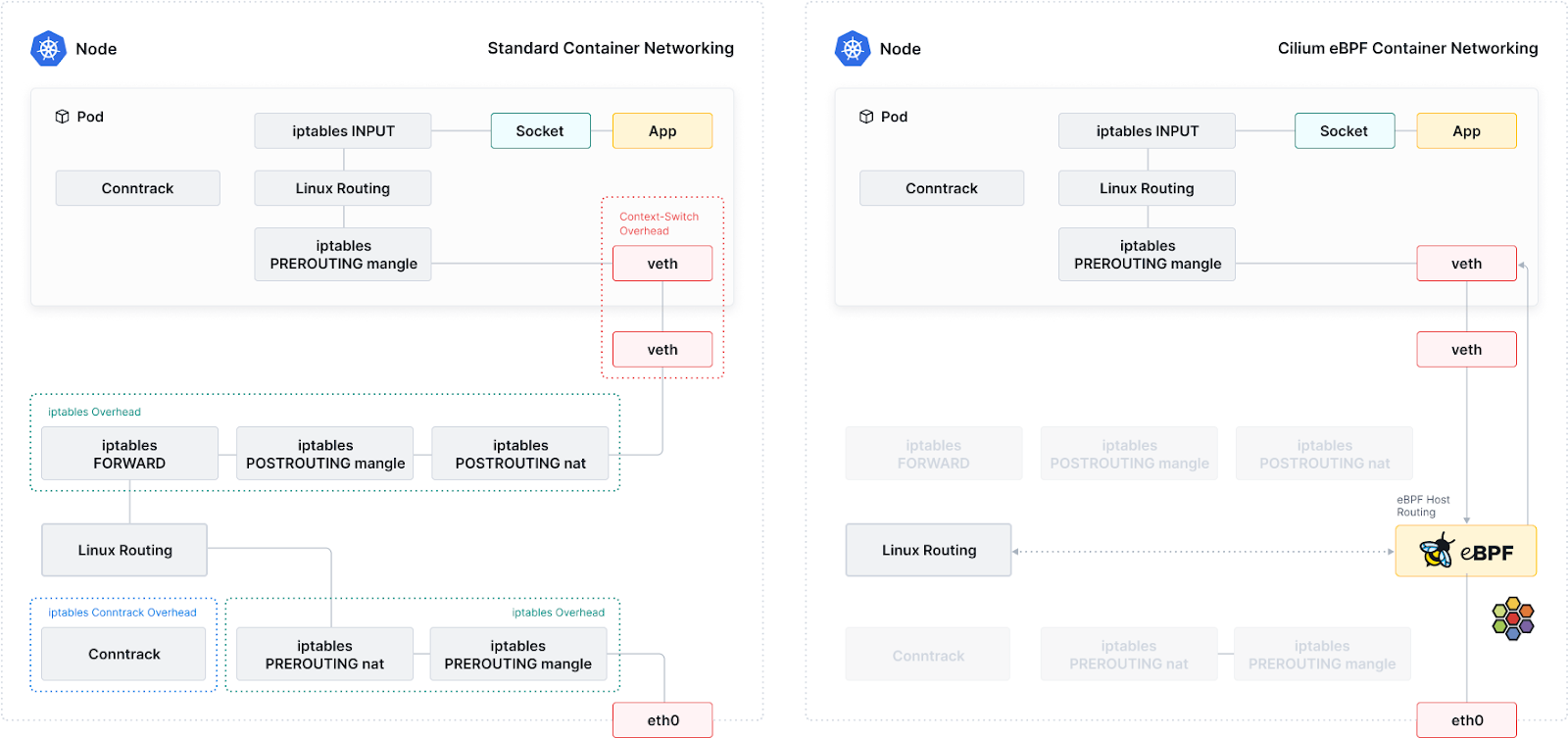
Cilium is an open source project that provides network-level security, observability, and runtime enforcement using eBPF. It enables fine-grained control over traffic and application behavior within Kubernetes and containerized environments. Cilium’s runtime capabilities include policy enforcement and transparent network visibility without requiring changes to workloads.
Key features include:
- eBPF-based enforcement: Enforces network and runtime policies directly in the kernel for performance and accuracy
- Transparent encryption and firewalling: Secures communication between workloads at L3/L4 with identity-aware policies
- Service mesh capabilities: Provides traffic control and observability without sidecars
- Cluster-wide observability: Offers visibility into network flows, service dependencies, and application behavior
- Support for multi-cloud and hybrid deployments: Scales across large, distributed Kubernetes clusters with low overhead
8. Tetragon
Tetragon is an eBPF-based runtime security and observability tool that integrates tightly with Kubernetes. Built as a sub-project of Cilium, it enforces policies at the kernel level and captures telemetry for threat detection. Tetragon tracks process execution, network activity, and file access, enabling synchronous policy enforcement without relying on user-space components.
Key features include:
- Kernel-level policy enforcement: Applies runtime controls directly in the kernel to block malicious actions immediately
- Kubernetes-aware observability: Associates events with Kubernetes metadata for contextual analysis
- Minimal performance impact: Uses eBPF for low-overhead monitoring across large-scale environments
- Event tracking: Monitors system calls, privilege changes, file access, and namespace activity
- Policy library and integration: Offers ready-to-use policies and supports output via logs or gRPC for external tools
Evaluating and Choosing a Runtime Security Tool
Visibility Depth and Data Sources
When evaluating runtime security tools, visibility depth is a critical factor. This refers to how thoroughly the tool inspects runtime activity, from kernel-level system calls to application-layer events. The best solutions capture a broad spectrum of events, including process activities, file accesses, and network connections, providing security teams with complete context for incident detection and investigation.
Data sources also play a key role in delivering actionable intelligence. Tools that integrate with orchestration platforms, application logs, and cloud APIs offer greater coverage and context. Security leaders should assess whether prospective tools can ingest diverse data, enrich alerts with relevant details, and maintain performance as environments scale.
Detection Techniques, Accuracy, and False Positive Management
Detection accuracy is paramount when selecting a runtime security tool, as overly sensitive detection can overwhelm teams with false positives and erode trust in the system. A quality solution offers precise detection logic, using contextual analysis, behavioral baselining, and machine learning to distinguish between benign activities and genuine threats.
False positive management is equally crucial, as a high signal-to-noise ratio enables efficient operations. Look for features such as customizable rules, suppression options, and the ability to tune sensitivity based on environment-specific baselines. The ability to correlate signals across multiple sensors and enrich alerts with context minimizes unnecessary alerts and ensures reported events are actionable.
Blocking and Mitigation Capabilities
Effective runtime security tools don't just detect threats—they also provide mechanisms to contain or prevent them in real time. Blocking capabilities can include killing malicious processes, isolating compromised containers, preventing unauthorized file modifications, or throttling suspicious network connections. These features help reduce the window of exposure and prevent lateral movement during active attacks.
Mitigation controls must be granular and configurable. Tools should support policies that allow security teams to define automated responses based on severity, workload type, or environment (e.g., staging vs. production). For example, a critical alert in production might trigger immediate blocking, while similar behavior in development could generate a non-blocking alert for investigation.
Additionally, runtime tools should log every mitigation action with context for auditing and post-incident analysis. The ability to simulate policy actions in “alert-only” mode before enforcement helps teams fine-tune rules and avoid unintended disruptions.
Integration and Scalability
A runtime security solution’s effectiveness is closely tied to its ability to integrate seamlessly with existing infrastructure and scale alongside the organization’s environment. Strong integration abilities include support for SIEM, SOAR, ticketing systems, and DevOps toolchains. This centralizes alert management, automates workflows, and promotes unified security operations across hybrid and multi-cloud deployments.
Scalability is vital as organizations adopt more microservices, containers, or cloud resources. The chosen tool should perform consistently across varying deployment sizes and support automated provisioning through infrastructure-as-code tools or orchestration platforms. Elastic licensing, cloud-native deployment options, and distributed architectures enable runtime security tools to remain effective as operational demands grow.
Performance Impact and Overhead
Performance overhead is a significant consideration in runtime security, as excessive resource consumption can degrade application performance or introduce unacceptable latency. The chosen tool must strike a balance between deep monitoring and efficient operation, leveraging lightweight agents, kernel modules, or sidecars without affecting process stability.
It’s important to assess runtime performance through trials and benchmarks relevant to the deployment’s workloads. Organizations should monitor CPU, memory, and network utilization introduced by the tool, examining whether monitoring can be selectively tailored as needed.
Compliance and Reporting Support
Many organizations rely on runtime security tooling to support compliance initiatives, such as PCI DSS, HIPAA, or GDPR. Security tools should offer comprehensive reporting features, detailed audit logs, event histories, and customizable dashboards, making it easier to demonstrate adherence to regulatory requirements.
Beyond regulatory needs, robust reporting helps prove internal policy adherence and supports continuous improvement. Leading runtime security platforms integrate with GRC tools, offer exportable logs, and allow scheduling of compliance summary reports.
Conclusion
Runtime security tools are essential for defending modern, dynamic environments where traditional perimeter-based protections fall short. By providing deep, continuous monitoring and enforcement at the execution layer, these tools help detect threats in real time, contain breaches, and maintain compliance in fast-changing infrastructures. As organizations scale their use of containers, microservices, and cloud-native technologies, runtime security becomes a critical component of a resilient and responsive security strategy.




